AGENDA
Booking Software for Tours & Activities
We know how time consuming coordinating reservations can be. Save money and increase sales by allowing your clients to book through your website 24/7.
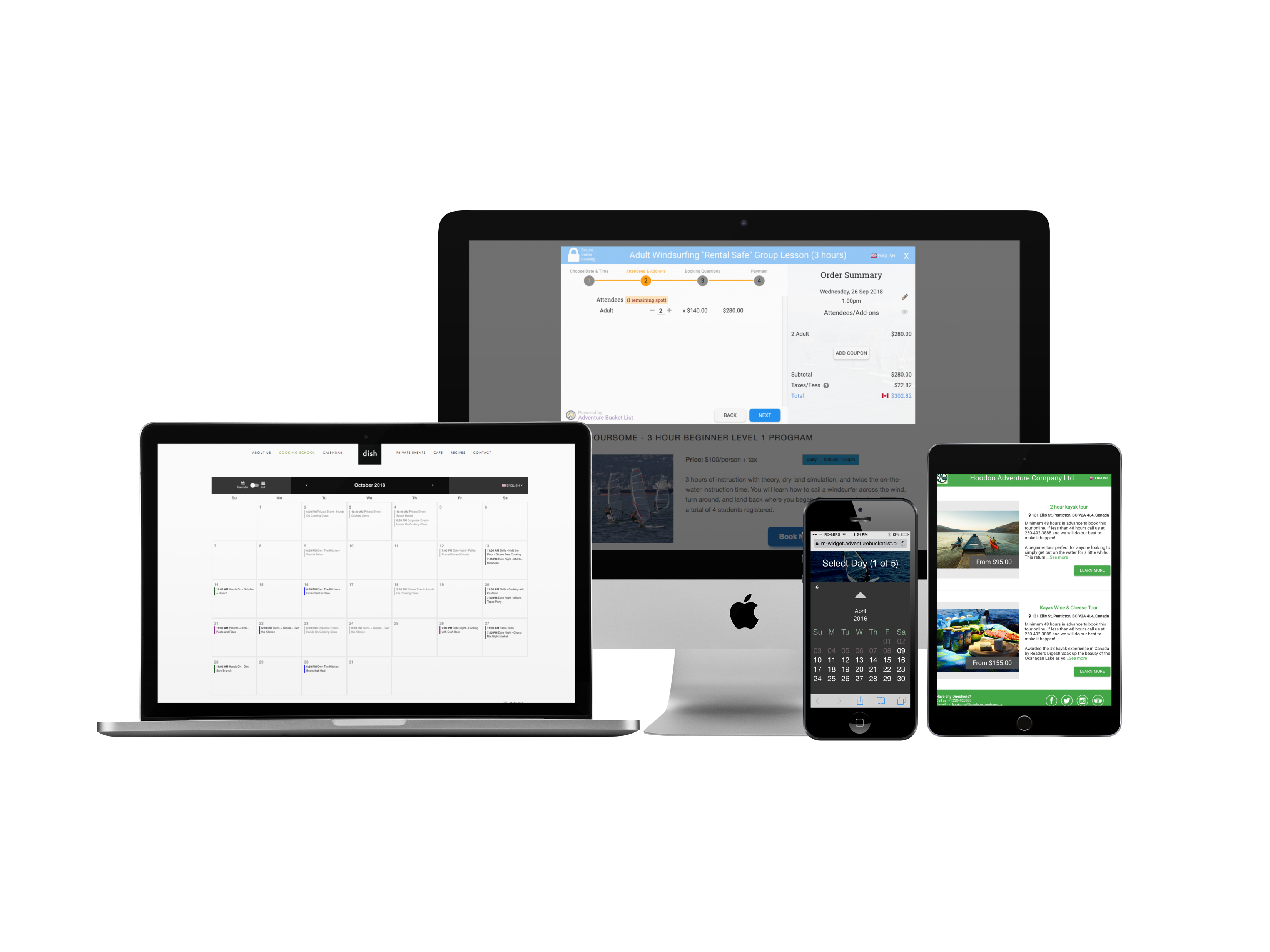
Fast & Easy Setup
Get setup and accepting bookings with a few minutes!
Get More Business
Allow your customers to book 24/7 and never worry about over-booking.

Built For YOU!
Click the image that best describes your business
User Reviews
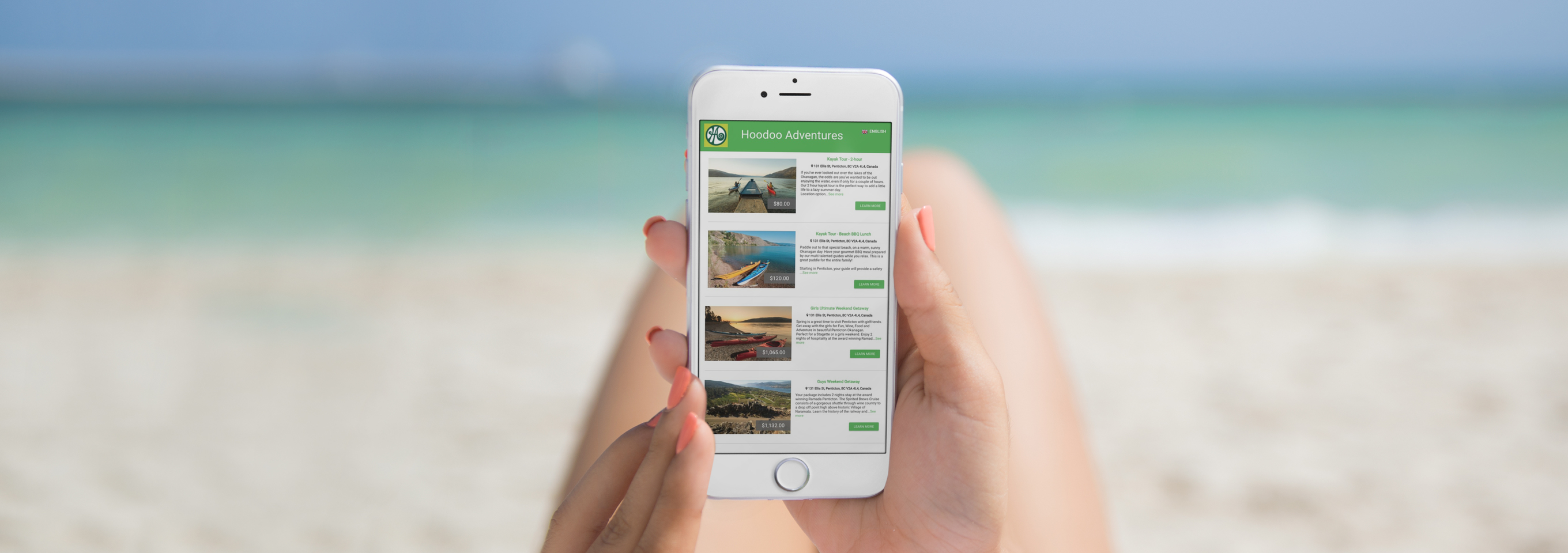
Let Your Customers Book From Anywhere
Our Booking buttons work on all devices so your customers can book from anywhere, anytimeSet your availability and let the bookings flow in
Compatible with all browsers and devices
SSL encrypted payments for ultimate security
Get automatic bank deposits
Accept Bookings 24/7 - Never miss a sale!
80% of travelers want to book outside of regular business hours. Let you clients book when it is convenient for them and never worry about overbooking.
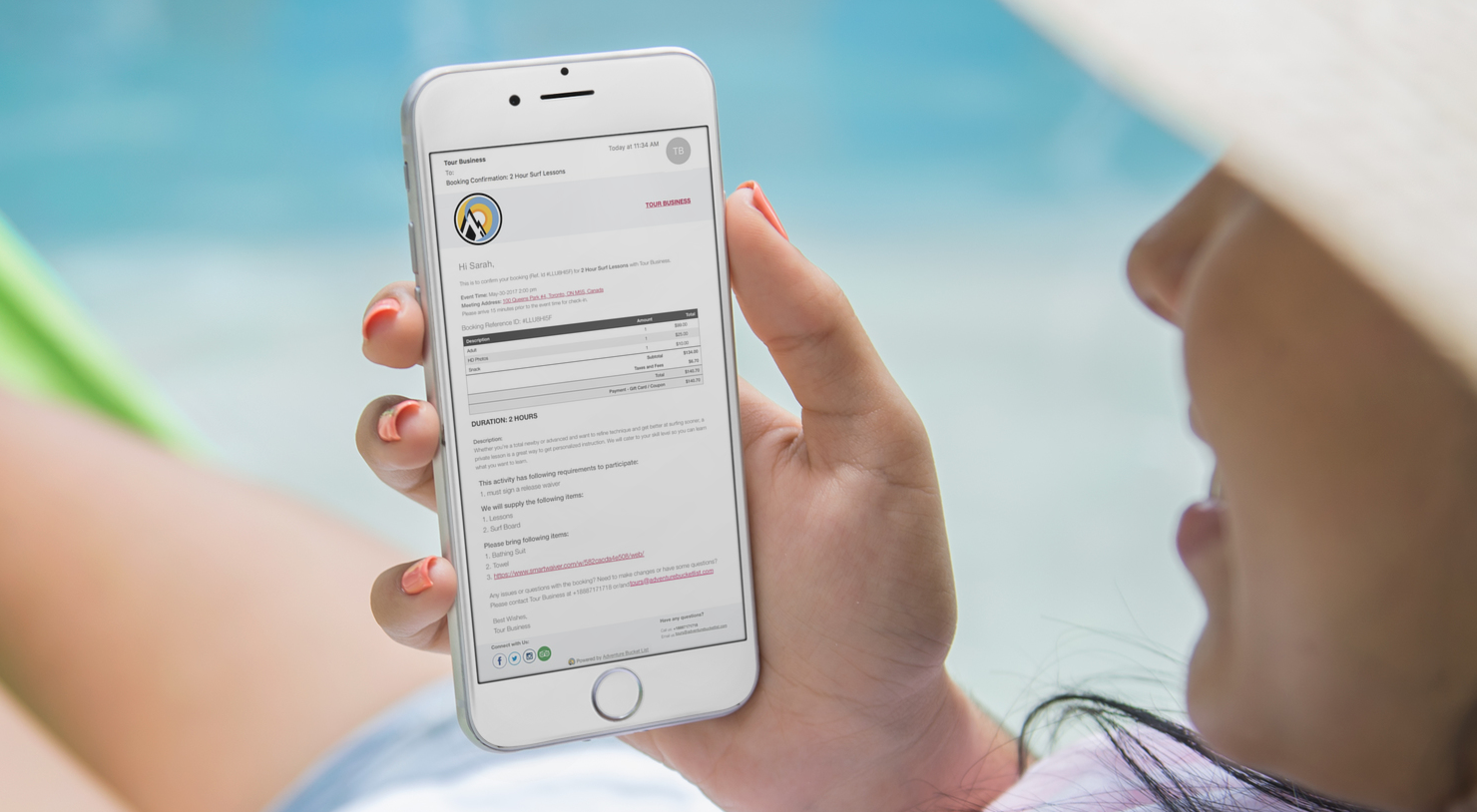
Save time with automated booking confirmations and trip follow ups
Booking confirmation emails are automatically sent with all the important details so you don't need to spend time writing emails. You can also activate follow-up emails thanking your clients and asking them to leave a Trip Advisor review.

Watch your business Grow!
Track all your online and offline revenue. Export financial data to csv files for easy accounting. Track your money from purchase until it is in your back account.